DigitStealer: New Campaign
- 3 mins
Intro
The Jamf Threat Labs team and Moonlock Labs recently published research on a new macOS infostealer, dubbed DigitStealer. DigitStealer, which has been active since at least November 2025, employs sophisticated new anti-analysis checks with the goal of stealing sensitive information such as browser data, cryptocurrency wallets, Keychain items, Telegram data and more from infected macOS systems.
This blog post highlights a continuation of that research, focusing on a updated campaign that continues to target Dynamic Lake users through a fake Dynamic Lake application, dubbed Apple Lake.
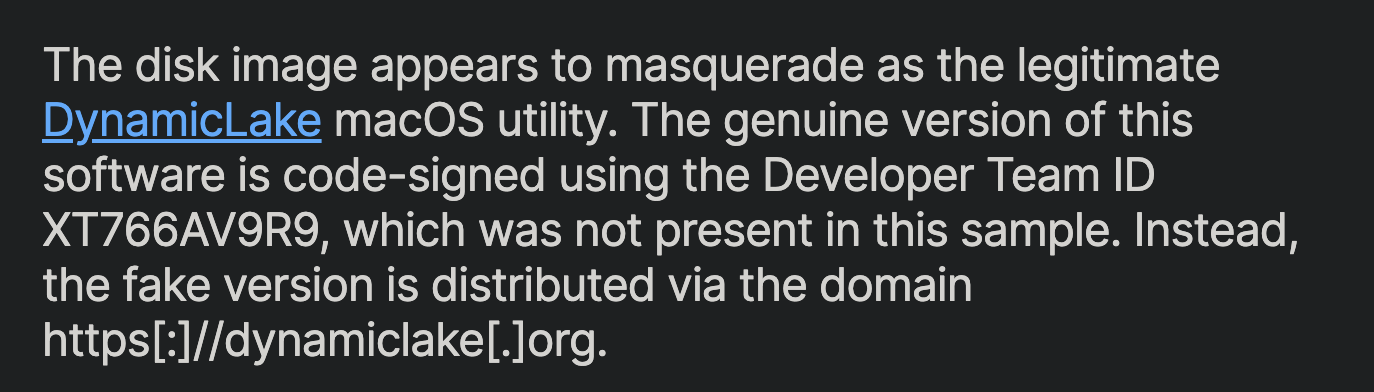
Dynamic Lake is a legitimate macOS application used for data visualization and analysis. The malicious campaign impersonates this application to trick users into downloading and executing the DigitStealer malware.
New Campaign Overview
In Jamfs original research, they identified a campaign distributing DigitStealer via a fake Dynamic Lake application hosted on the domain dynamiclake[.]app. Pivoting from that domain, I discovered activity indicating a new campaign distributing DigitStealer through a similarly named domain, applelake[.]app, and clearmacos[.]com.
 Source: Jamf Threat Labs
Source: Jamf Threat Labs
Heading to URLScan, I searched for dynamiclake[.]app. Pivoting to the indicators, I discovered a hash that stood out: 03139d93b706947a8144978abd70c511587a441d1baf76a40eff9c9dd1fc9a53.
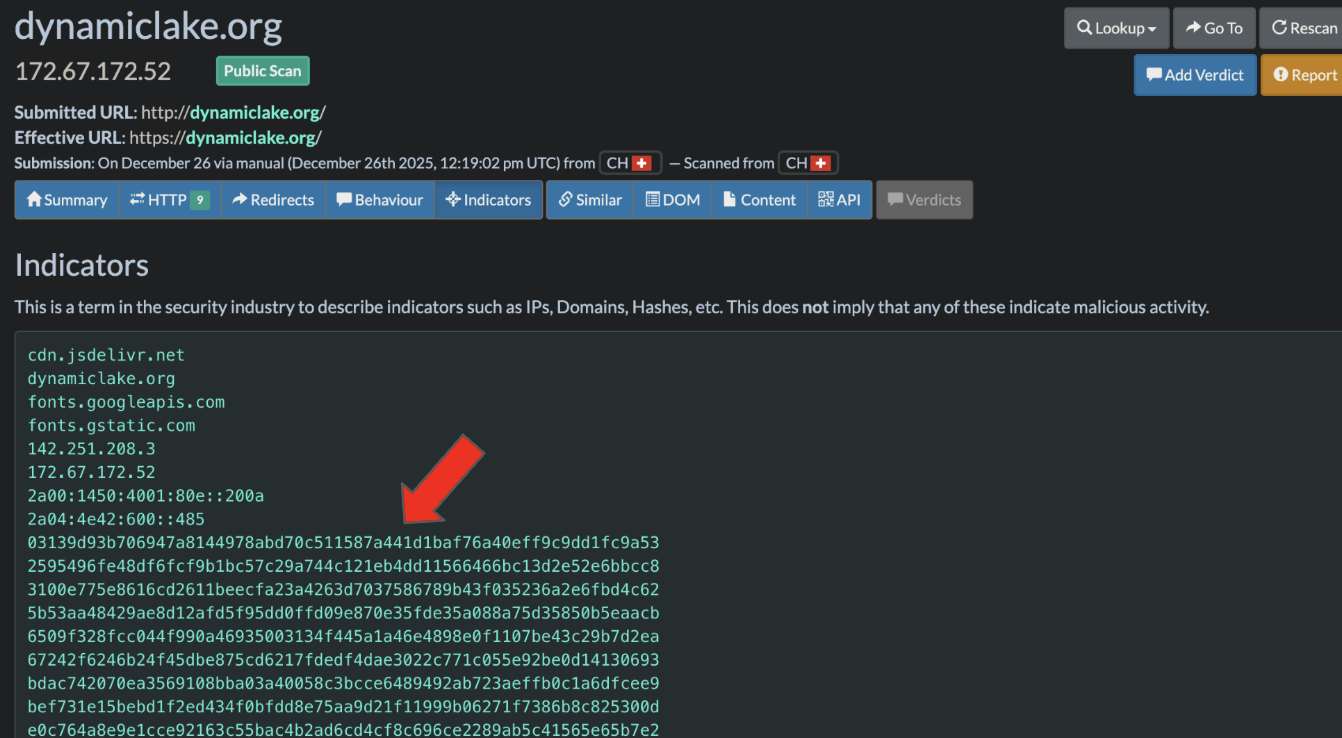
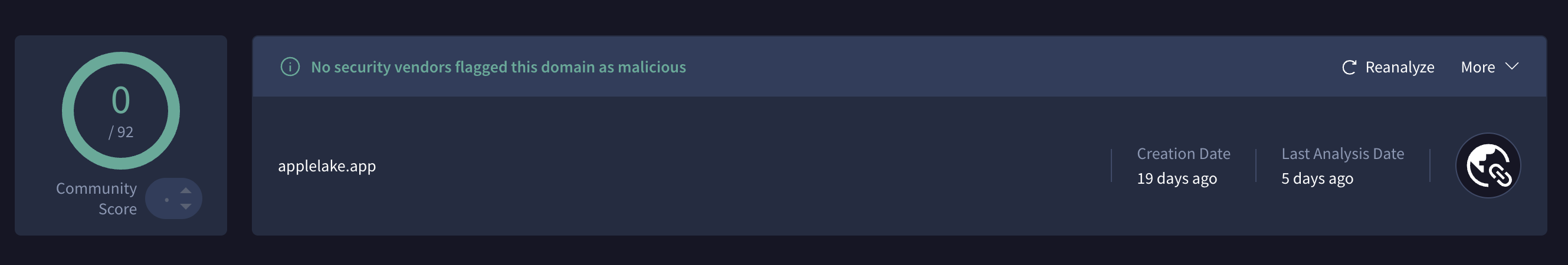
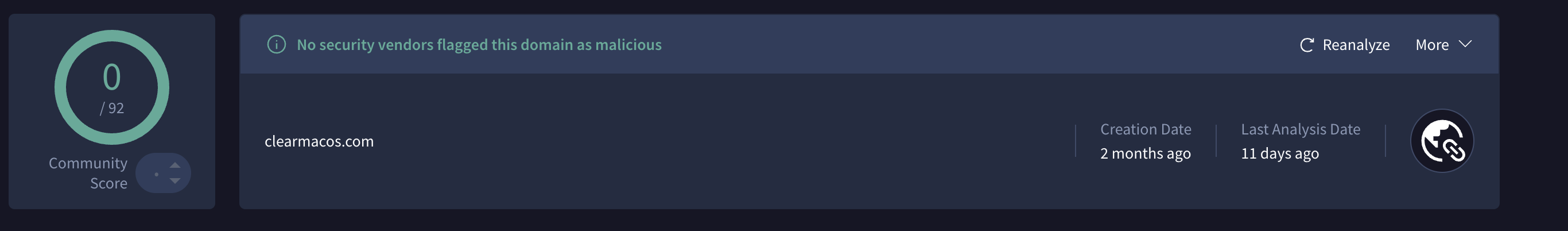
This hash corresponds to two new domains, submitted in the past 2 weeks: applelake[.]app and clearmacos[.]com.
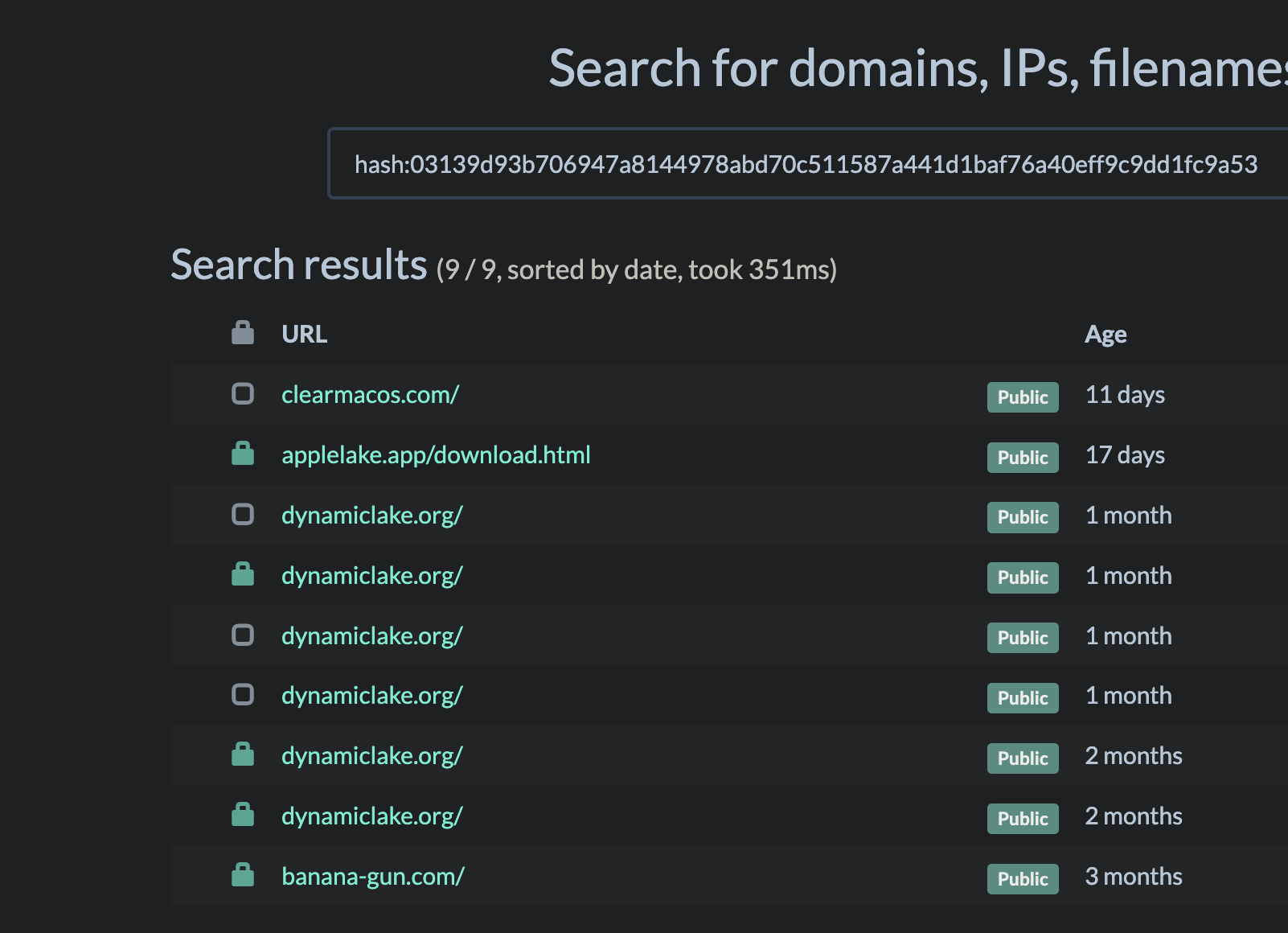
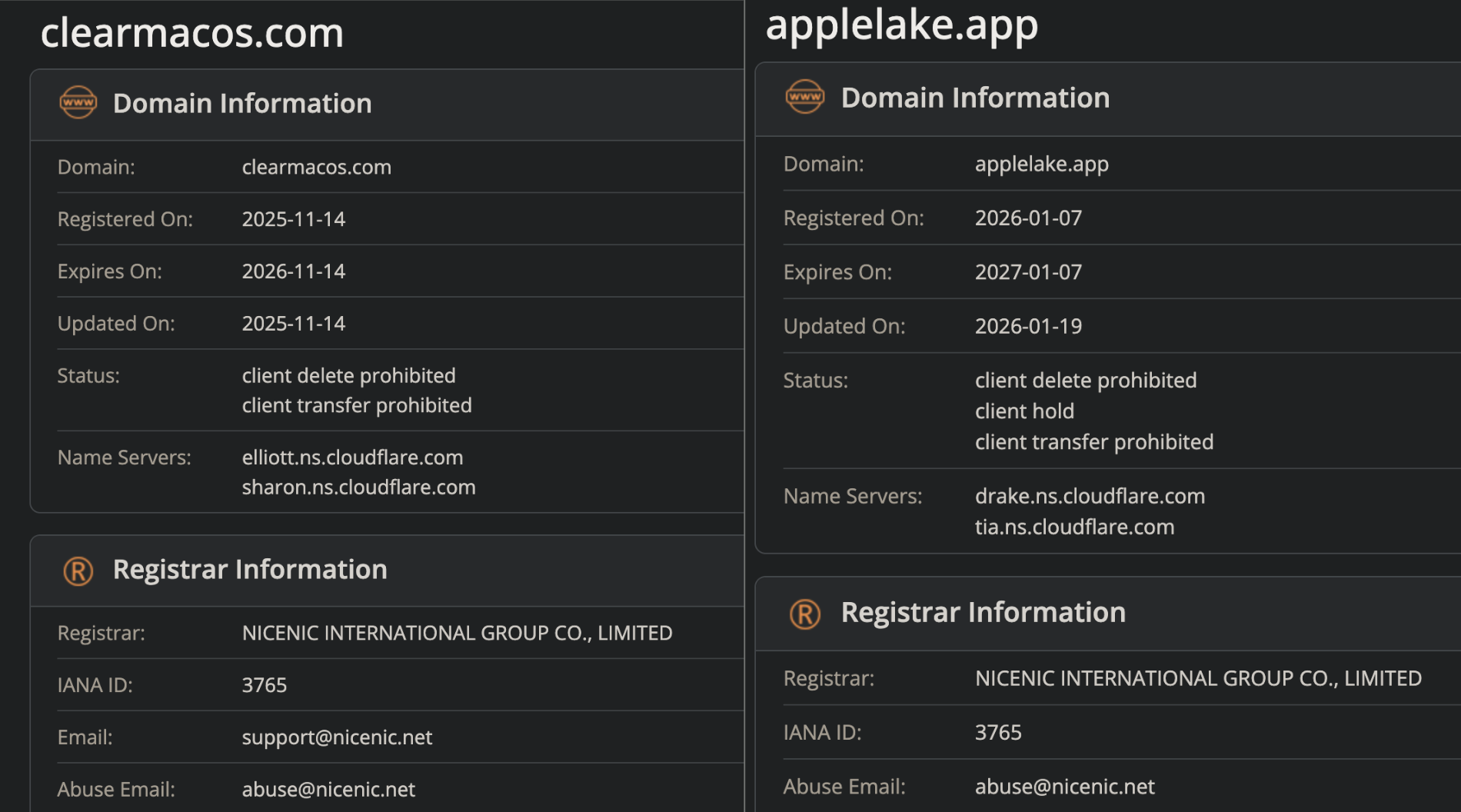
Both domains share similar infrastructure, as being registered via NICENIC, and hosted on Cloudflare.
Dorking around, I came across a Reddit thread where multiple users reported being targeted by this new campaign. It appears this campaign is actively distributing DigitStealer via Youtube ads/videos - one such video (now unlisted) can be seen here. The video in question points to another domain, applelake[.]org.
A user by the name of GooseIsChaos chimes in the thread and points out distinct similarties between Applelake and DigitStealer. They provide their own analyis, all of which can be seen here.
A common TTP amoung macOS stealers is the use of malvertising/leveraging Traffers to spread their malware, and DigitStealer appears to be no different. At the time of publication, both applelake[.]app and clearmacos[.]com are both undected in Virustotal.
Further pivoting on the “Applelake.dmg” name, I came across recent analysis and research by L0PSec, MalwareHunterTeam, and others on Twitter, all pointing different samples, but the same campaign.
Looks like MacSync. C2 in the info.plist. Uses simple XOR calls throughout for all strings, that are then passed to snprintf() for replacing format strings and finally system() for exec.
— L0Psec (@L0Psec) January 24, 2026
Let's take a quick look for fun as the winter storm approaches. 🌨️
🧵 https://t.co/1bcRTnGVFe pic.twitter.com/Giw1oVkbYN
Conclusion
DigitStealer continues to target users by masquerading as Dynamic Lake, a legitimate macOS application. The new campaign leverages fake domains such as applelake[.]app and clearmacos[.]com, distributed via Youtube ads and videos. For both enterprise and individual users, using an adblocker such as uBlock Origin Lite can help mitigate the risk of encountering such malvertising campaigns.
Indicators of Compromise (IOCs)
- applelake[.]app
- clearmacos[.]com
- applelake[.]org
- 03139d93b706947a8144978abd70c511587a441d1baf76a40eff9c9dd1fc9a53 (URLScan Hash)
- b8b690adf33b05342f769909fb0b3aca819ce8d5da304a80df4bfdb91ef54a1f (Applelake.dmg)